12 Min Read
Every lending leader carries a version of the same quiet frustration.
They know that tightening fraud controls will cost them conversion.
They know that the automation their ops team pushed for has created blind spots that keep surfacing in audits.
They know that the speed their product team demanded came at the cost of documentation their compliance team now can't reconstruct.
These aren't failures of execution. They're the natural consequence of building lending systems under competing pressures - and making implicit tradeoffs rather than explicit ones.
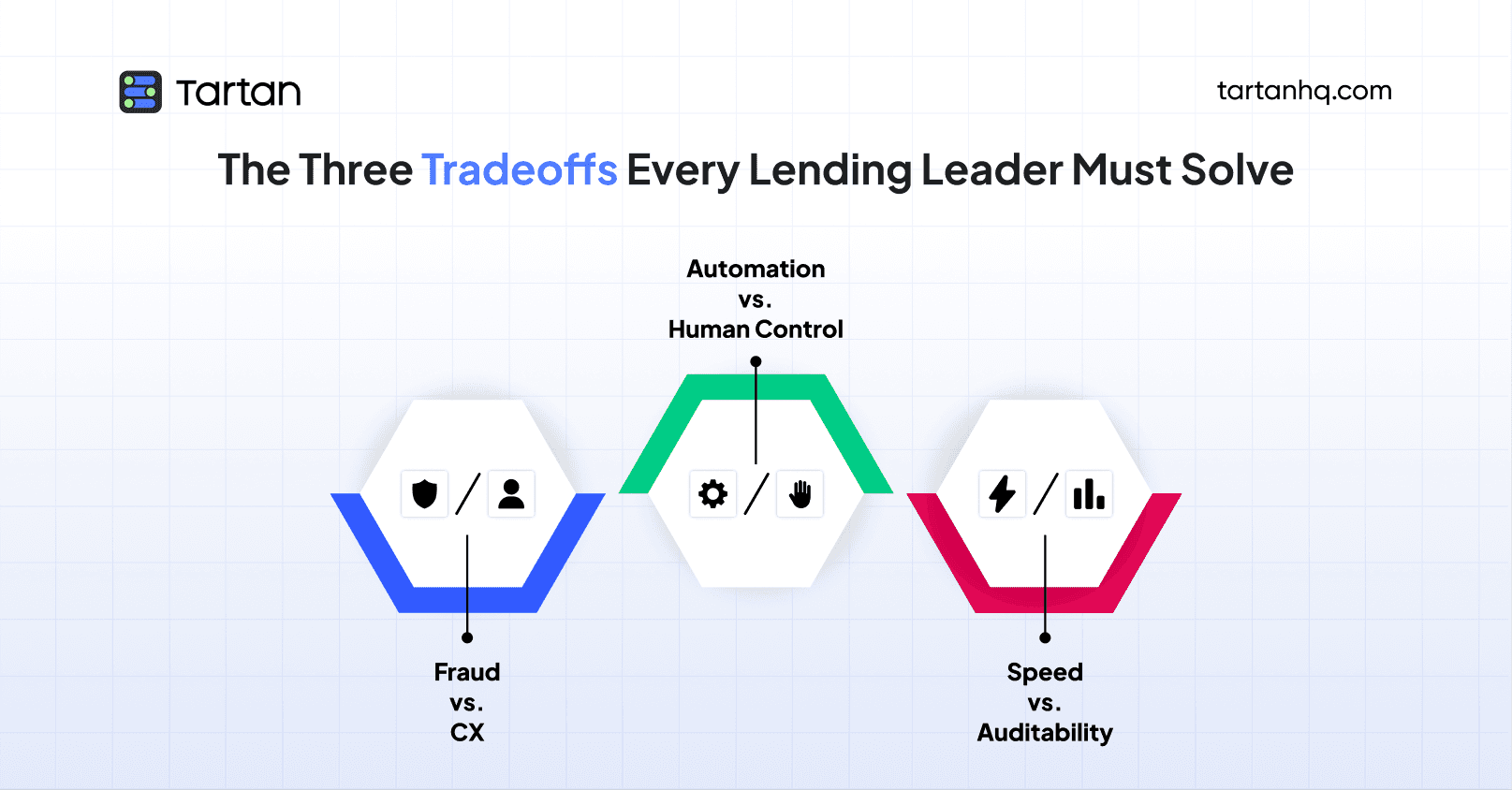
The three tradeoffs at the centre of modern digital lending - fraud prevention versus customer experience, automation versus human control, speed versus auditability - don't have clean resolutions. But they do have better and worse ways of being managed. The lenders building durable, scalable credit businesses are the ones who've stopped pretending these tensions don't exist and started designing around them deliberately.
This piece is for the lending leaders who are ready to do that.
Tradeoff One: Fraud Prevention vs. Customer Experience
This is the tension every product and risk team knows intimately, and it's the one that generates the most internal conflict.
The fraud prevention instinct says: add more checks. More document verification steps. More liveness detection layers. More manual review queues. More friction between the applicant and the loan. Every additional checkpoint is another opportunity to catch a bad actor before they cost you money.
The customer experience instinct says: remove friction. Borrowers have options. A competitor's app is three taps away. Every additional step in the application flow is a drop-off risk. Every manual review adds latency that translates to abandonment. The best KYC is the one the customer barely notices.
Both instincts are right. That's what makes this genuinely hard.
The mistake most lenders make is treating this as a dial - more fraud prevention means less CX, and you simply choose where on the dial you want to sit. That framing is wrong, and it leads to bad decisions.
The real question isn't how much friction to add. It's where in the borrower journey friction is tolerable, and where it isn't.
A borrower applying for a ₹50,000 personal loan for the first time has relatively high tolerance for verification steps. They expect it. They're asking for money from someone who doesn't know them - some level of identity confirmation feels reasonable. The CX damage from a thorough onboarding check is lower than most product teams assume, provided the experience itself is well-designed.
That same borrower, fourteen months later, requesting a ₹20,000 top-up on a loan they've been repaying faithfully, has almost zero tolerance for friction. They're an established customer. They have a track record. Putting them through a near-full re-KYC at that moment is not just operationally unnecessary - it's a signal that you don't recognize them, that the relationship doesn't matter. That's where CX damage is real and conversion impact is significant.
The resolution to this tradeoff isn't less fraud prevention - it's fraud prevention that's calibrated to context. High-friction controls where the risk justifies them. Low-friction, background verification where the customer has earned trust. Risk-based authentication that scales with the sensitivity of the transaction, not with the lender's operational convenience.
The lenders who get this right have stopped applying uniform verification intensity across every touchpoint and started building verification that's proportionate to the moment. They protect hard at new exposure events. They stay light - but not blind - at low-risk, high-familiarity moments.
The lenders who get it wrong are applying the same document-heavy process to a routine top-up that they apply to first-time origination. They're losing customers they didn't need to lose, and they're not getting meaningfully more fraud protection in return.
Tradeoff Two: Automation vs. Human Control
Automation in lending operations was supposed to solve everything: faster decisions, lower ops costs, reduced human error, infinite scale. And in many ways, it has. Rule-based decisioning, API-first verification, automated bureau pulls - these have genuinely transformed what a lean lending team can process.
But automation has a failure mode that's harder to see until something goes wrong: it doesn't know what it doesn't know.
A well-configured automated decisioning system is excellent at catching the cases it was trained to catch. It struggles with edge cases, novel fraud patterns, and the kind of contextual signal that an experienced underwriter would flag but that never made it into the rules logic. It also creates a particular organizational risk: over time, the institutional knowledge of why the rules are the way they are erodes. The people who built the system leave. The documentation is incomplete. What remains is a system that produces decisions nobody fully understands anymore.
This is the automation trap. And lending teams fall into it gradually, usually because the economics of automation are so compelling that the incentive to keep humans in the loop gets steadily squeezed out.
The counterpoint - that human underwriting is slower, more expensive, and introduces its own inconsistencies - is entirely valid. Manual review queues create latency. Human reviewers make subjective decisions that are hard to audit. Consistency suffers at scale.
So where does the resolution sit?
The most effective lending operations today aren't choosing between automation and human control - they're designing for what each does well. Automation handles volume, consistency, and speed at the clear cases on both ends of the risk spectrum: the clean approvals and the obvious declines. Human judgment is reserved for the middle - the cases where the automated signal is ambiguous, where the context matters, where the decision has meaningful consequences if it goes wrong.
The critical design principle is that automation should be legible. Every automated decision should be reconstructible: what data was used, what rules fired, what the output was, and why. Not because regulators will always ask - though increasingly they will - but because a system you can't interrogate is a system you can't improve. When your NPAs tick up, you need to be able to trace back which decision logic is responsible. Opaque automation denies you that.
The other critical principle is feedback loops. Automated systems degrade silently if the outcomes aren't fed back into the rules. A fraud pattern that first appeared six months ago and is now systematic may not be in your rules logic at all - because nobody noticed it when it was new, and the automation kept approving cases that fit the pattern. Human review of edge cases and exception reports is the mechanism by which automation learns. Remove the humans, and the system stops getting smarter.
The tradeoff between automation and control isn't resolved by choosing a side. It's resolved by being deliberate about where each belongs - and building the feedback infrastructure that keeps automated systems honest over time.
Tradeoff Three: Speed vs. Auditability
Speed is the most celebrated virtue in digital lending. TAT compression - reducing the time from application to disbursement from days to hours to minutes - is one of the genuine competitive advantages the digital lending model has over traditional banking. Borrowers value it. It drives conversion. It's a legitimate product differentiator.
Auditability is speed's quiet antagonist. Every step in the verification and decisioning process that gets documented, logged, and retained for regulatory review is a step that adds some operational weight. Comprehensive audit trails require data infrastructure. Compliance documentation requires process discipline. Regulatory reporting requires that decisions made at speed are still reconstructible months or years later.
The tension isn't theoretical. Teams under pressure to hit TAT targets make expedient choices - skipping documentation steps, approving manual overrides without logging rationale, relying on verification outputs that aren't being retained in a form the regulator can actually inspect. Those choices accumulate.
And when the audit comes, or when the fraud case surfaces and the legal team needs to reconstruct the decisioning sequence, the gaps are suddenly very expensive.
But the more important reason to care about auditability isn't regulatory - it's operational. An audit trail is the memory of your lending operation.
It's how you know which loan products are performing, which customer segments are drifting, which verification steps are actually predictive of default versus which are just adding friction without risk value. Without that data, you're managing a lending book by intuition and lagging indicators.
The resolution to this tradeoff requires a reframe. Speed and auditability are not naturally opposed if the systems doing the work are designed to log by default. The reason they feel opposed in practice is that most lending operations have bolted documentation onto existing processes rather than building it in. When logging is an afterthought, it creates friction. When it's native to the system, it's nearly invisible.
The practical implication is that lending teams should be highly skeptical of any verification or decisioning tool that doesn't produce a clean, exportable audit record by design. Speed without a trail isn't an asset. It's a liability waiting to surface.
Why These Tradeoffs Are Connected
It would be convenient if these three tensions operated independently - if you could solve fraud vs. CX without touching your automation architecture, or improve auditability without affecting speed. In practice, they're deeply interconnected.
A fraud prevention system that can't be audited is a fraud prevention system you can't improve. An automation stack that runs without human feedback loops will eventually optimize for the wrong things. A speed-first culture that dismisses documentation will find itself unable to reconstruct the decisions that drove the losses it's now trying to explain.
The lenders building the most resilient operations aren't winning on any single dimension. They're managing all three tradeoffs deliberately - with explicit policies rather than implicit defaults, with systems that are legible rather than opaque, and with verification infrastructure that's proportionate to risk rather than uniform across every context.
That's a harder operating model to build. But it's the one that compounds over time rather than accumulating hidden liabilities.
How Tartan's HyperVerify Helps Lending Teams Navigate All Three
Tartan built HyperVerify with these tradeoffs in mind - not as a verification tool that optimizes for any single one, but as a platform that helps lending teams make better decisions across all three.
On fraud vs. CX: HyperVerify enables risk-proportionate verification across the borrower lifecycle. At onboarding, it runs thorough identity, address, and employment checks. At top-up and limit enhancement events, it executes lightweight but real-time verification refreshes - confirming address currency, mobile number validity, and employment signals - without putting established borrowers through a full re-KYC. The friction is calibrated to the context, not applied uniformly.
On automation vs. control: HyperVerify's verification outputs are designed to be legible and actionable - not black-box scores but structured signals that tell underwriting and risk teams what was checked, what was confirmed, and what flagged. It integrates into automated decisioning flows while preserving the ability for human reviewers to interrogate the underlying data. Edge cases surface with context, not just an exception flag.
On speed vs. auditability: Every verification event run through HyperVerify generates a complete, timestamped audit record - what data sources were queried, what was returned, what decision was supported. That record is available for compliance documentation, regulatory reporting, and internal portfolio analysis. The speed of API-first verification isn't sacrificed; the audit trail is native to how the system works, not bolted on afterward.
For lending teams that have been managing these tradeoffs through improvised workarounds and competing team priorities, HyperVerify by Tartan provides the infrastructure to manage them through design instead.
The three tradeoffs in digital lending don't disappear. But they become significantly more manageable when the systems you're building on are designed to hold them in tension deliberately - rather than collapsing one side in the name of operational convenience.
Tartan helps teams integrate, enrich, and validate critical customer data across workflows, not as a one-off step but as an infrastructure layer.