10 Min Read
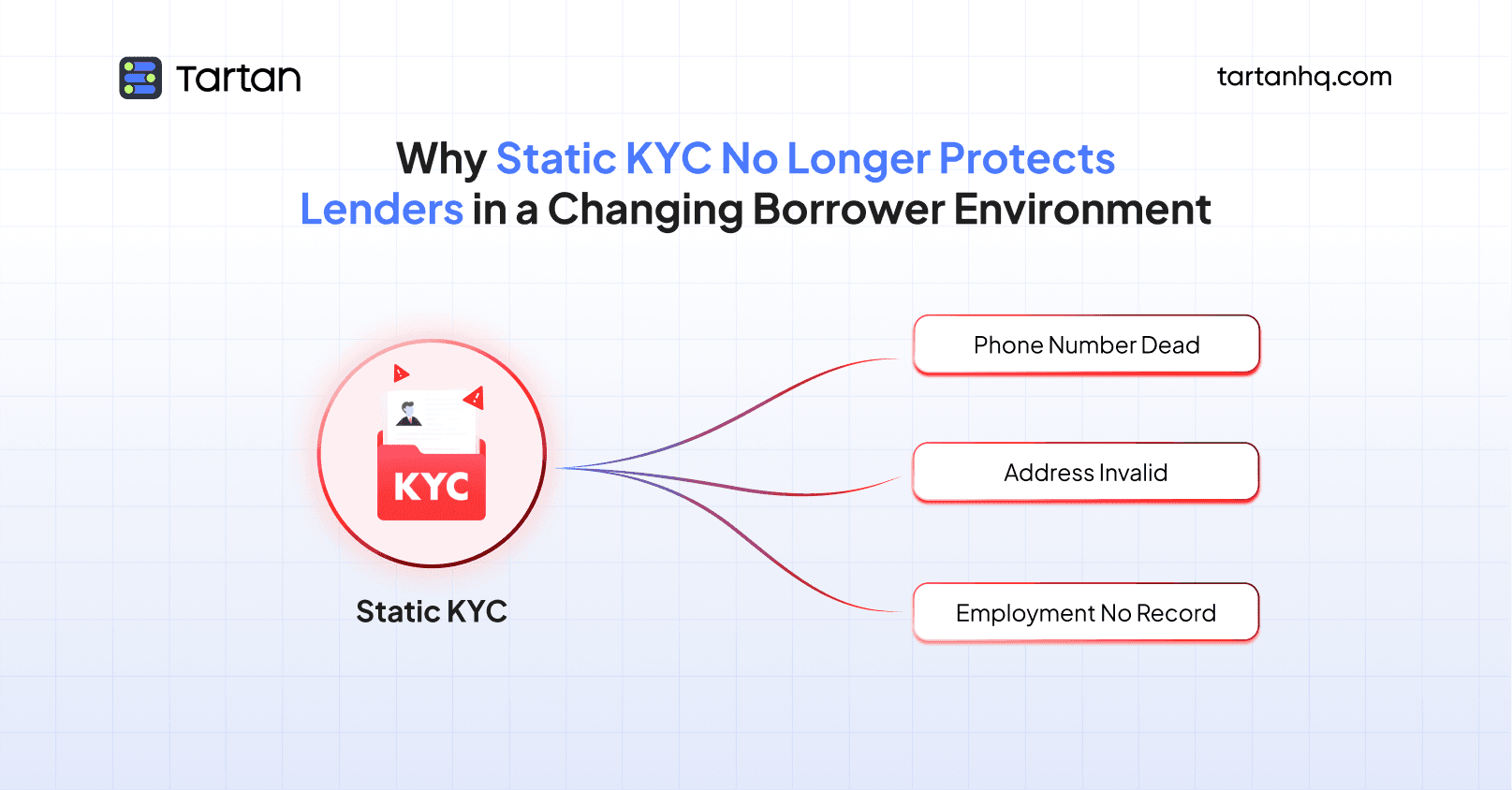
There's a moment every credit risk manager recognizes. A borrower who looked perfectly underwritten at origination - stable employment, verified address, clean bureau - surfaces in the 90+ DPD bucket eighteen months later.
Collections reaches out.
The phone number is dead.
The address goes to a different city.
The employer? No record of the person.
The instinct is to call it a fraud case. Sometimes it is. But more often, it's something subtler and more systemic: the borrower's life changed, and the lender's data didn't.
This is the central failure of static KYC in a dynamic borrower lifecycle - and it's a failure that lending teams are only beginning to reckon with seriously.
What "Static KYC" Actually Means - and Why It's Structurally Broken
KYC, as practiced by most digital lenders, is a point-in-time exercise. At origination, a borrower submits identity documents, completes a liveness check, links their bank account, and provides employment and address details. That data is verified, filed, and - in the overwhelming majority of cases - never substantively updated again.
The industry term for this has evolved.
What used to be called KYC has expanded into KYX: Know Your Customer, Know Your Employee, Know Your Business, depending on the context. But regardless of the label, the underlying architecture is the same. One verification event at the start of the relationship. A static record that the entire lending lifecycle runs on top of.
This made reasonable sense in a world of long-tenure, low-churn borrowers - say, a salaried professional in a metro city taking a three-year personal loan. The assumption was that the person who showed up on day one would be roughly the same person on day 900.
That assumption doesn't hold for India's digital lending market in 2024.
The average tenure of a digital consumer loan has compressed. Borrower profiles are increasingly from non-metro markets, gig and informal employment, and demographics with higher life-event volatility. Layoffs, relocations for work, business closures, family changes - these aren't edge cases in the borrower population. They're the norm. And yet the verification infrastructure treating these borrowers as static entities captured once and filed away.
The gap between what's on file and what's actually true grows with every month of the loan lifecycle - and that gap is where credit risk quietly builds.
Employment Change: The Risk Signal Nobody's Monitoring
Of all the life events that materially affect credit risk, employment change is the most consequential and the least monitored.
Consider the mechanics.
A borrower takes a ₹4 lakh personal loan based on a verified salary of ₹65,000 per month from a mid-sized IT firm. That employment verification - a salary slip, a bank statement showing credits, perhaps an employer API check - is clean. The loan is approved.
Eight months later, the borrower is laid off. Or leaves voluntarily for a startup that pays less. Or transitions into freelance work. Their income drops materially. Their repayment capacity changes.
None of this shows up in your system.
The bank statement data you have is from onboarding. The employment verification is from origination. The bureau score is a lagging indicator - it reflects repayment behavior, not income events. By the time a missed payment signals distress, you're already in early delinquency. The employment change that caused it happened months ago and was invisible to you throughout.
This isn't hypothetical. The technology exists today to monitor employment signals - company-level data, PF contribution continuity, EPFO records, bank statement transaction pattern changes - on an ongoing basis rather than as a one-time snapshot. But most lenders aren't using it systematically, because their verification architecture wasn't built for ongoing monitoring. It was built for onboarding.
The result is a lending model that prices risk based on a borrower's situation at origination, then essentially flies blind through the actual repayment period - precisely the window where that risk either materializes or doesn't.
Relocation: The Address Problem Is Bigger Than Collections
Address staleness is typically framed as a collections problem: agents can't find borrowers, field visits fail, letters go undelivered. That framing is accurate but undersells the issue.
Address data in a lending file serves multiple functions. It's a fraud signal at origination. It's a geolocation input for risk scoring. It's a compliance anchor for regulatory reporting. It's a recovery tool in collections. It's a verification input for top-ups and limit enhancements.
When address data goes stale - which it does, continuously, across any lending book with a tenure beyond twelve months - all of these functions degrade simultaneously.
The scale of address churn in India is genuinely underappreciated. Internal migration rates are high. Rental markets in tier-1 and tier-2 cities turn over rapidly. Seasonal and occupational migration is common in the demographics that form a large portion of the digital lending market. A borrower living in a PG accommodation in Pune when they took a loan eighteen months ago may now be in Indore, Nagpur, or back in their home district.
None of this is inherently suspicious. People move. The problem is that lenders treat the address captured at onboarding as a durable fact rather than a snapshot of a moment in time.
The downstream consequences are significant:
For top-ups and limit enhancements: If a borrower's actual address has changed but their profile hasn't been updated, any address-based risk signals at re-underwriting are running on stale data. You're not catching the relocation to a lower-income geography. You're not flagging the move to a new city that coincides with a job change.
For fraud detection: Address verification at onboarding is partly designed to confirm that the person exists where they say they do. At top-up, if you're not re-verifying address, you're assuming the original signal still holds - even if the account has been taken over and the contact details quietly updated.
For regulatory compliance: Some regulatory frameworks require lenders to maintain current borrower address data. Periodic re-verification isn't just operationally useful - it has a compliance dimension that lending teams often overlook until an audit surfaces the gap.
Re-Verification Triggers: The Framework Lenders Are Missing
The core problem with static KYC isn't that lenders don't understand the risk of stale data. Most credit risk professionals understand it intuitively. The problem is that they lack a structured framework for when and how to re-verify - so re-verification either doesn't happen, or happens haphazardly.
What the industry needs, and is slowly beginning to build, is a trigger-based re-verification framework: defined events in the borrower lifecycle that automatically initiate a verification refresh.
The most important triggers fall into three categories:
Product events. Top-up loan requests. Limit enhancement applications. Loan restructuring. Tenure extensions. Any time a lender is making a new credit decision about an existing borrower, they are implicitly re-underwriting that borrower - and re-underwriting should include re-verification of the data underpinning that decision. Approving a top-up based on address and employment data that is fourteen months old is not meaningfully different from not verifying at all.
Behavioral signals. Changes in repayment pattern. A shift from auto-debit to manual payment. A sudden address or phone number update in the borrower app. Device changes. Login location anomalies. These behavioral events are already visible in most lenders' systems - they just aren't systematically connected to a re-verification workflow. When a borrower updates their registered mobile number, that should trigger an identity freshness check, not just an OTP to the new number.
Time-based triggers. Beyond events, there's a case for calendar-based re-verification for loans beyond a certain tenure. A borrower fourteen months into a twenty-four month loan has a relationship with you that predates significant potential life changes. A lightweight periodic check - address currency, mobile number validity, employment signal monitoring - doesn't need to be a full KYC re-do. It needs to be enough to flag material drift.
Building this framework requires two things that most lenders currently lack: a clear policy for what triggers re-verification, and a technical capability to execute re-verification quickly and cheaply enough that it doesn't create operational drag.
The Cost of Not Acting
The case for dynamic verification is sometimes framed primarily as a fraud prevention argument. That framing is incomplete.
Fraud is the dramatic version of the risk. But the quieter, more prevalent cost of static KYC is credit loss that isn't fraud at all - it's just risk that changed and wasn't tracked.
A borrower who loses their job six months into a loan is not a fraudster. But if the lender had employment monitoring in place, they might have caught the income signal change early enough to trigger a proactive collections conversation, offer a restructuring, or at minimum, not approve the top-up request that came in two months before the first missed payment.
That's the cost of static KYC: not just the fraud cases that slip through, but the ordinary credit deterioration that could have been caught - and managed - earlier.
At the portfolio level, this isn't a marginal difference. Across a lending book of any meaningful scale, the combination of undetected employment changes, stale address data, and missed re-verification triggers represents a material drag on recovery rates and collection efficiency. The lenders who close this gap will have a structural cost-of-risk advantage over those who don't.
How Tartan's HyperVerify Closes the Gap
This is exactly the problem that Tartan built HyperVerify to solve.
HyperVerify is a dynamic identity and data verification platform designed for the full lending lifecycle - not just the onboarding moment. It enables lending teams to move from a static, point-in-time verification model to a continuous, trigger-responsive one - without rebuilding their existing tech stack.
For employment verification, HyperVerify offers ongoing employment signal monitoring through EPFO data, bank statement pattern analysis, and employer-level signals - surfacing income events between underwriting periods so lenders aren't flying blind through the repayment window. If a borrower's PF contributions stop, that's a signal. HyperVerify surfaces it.
For address verification, HyperVerify provides real-time address currency checks against authoritative databases at any point in the lifecycle. Before a top-up is approved. Before a collections file is escalated to field. Before a limit enhancement goes through. Not just at onboarding.
For re-verification triggers, HyperVerify integrates with lenders' loan management and collections systems to execute verification refreshes at defined trigger points - product events, behavioral anomalies, and periodic calendar-based checks - automatically and via API, without adding manual underwriting overhead.
For collections intelligence, HyperVerify enriches hard-to-reach accounts with current contact and address data, improving first-contact rates and helping lenders meet their regulatory documentation requirements for outreach attempts.
The result is a lending operation where the borrower data driving decisions is continuously validated rather than archived at origination. Where employment changes surface before they become missed EMIs. Where address drift is caught before it becomes a field recovery failure.
Static KYC was built for a static borrower. India's digital lending market doesn't have those. HyperVerify by Tartan is the infrastructure layer for the one it does.
The borrower lifecycle is dynamic. Your verification architecture should be too. Re-verification isn't a compliance checkbox - it's a credit risk function that the industry has been systematically under-investing in. The lenders who fix that first will carry it as a durable advantage.
Tartan helps teams integrate, enrich, and validate critical customer data across workflows, not as a one-off step but as an infrastructure layer.